FIPS and the Quiet Revolution in Mesh Networking

What Is FIPS?
FIPS stands for Free Internetworking Peering System. It is an open-source mesh networking protocol that allows devices to connect directly to each other without relying on internet service providers, DNS servers, certificate authorities, or any central infrastructure whatsoever.
The project was built by Arjun, who also works on the TollGate project, and Jonathan Corgan, described as an early presence on the Cypherpunk's mailing list with deep cryptographic expertise. Arjun met Jonathan at a Nostr conference in Costa Rica and the two spent days working through the idea of using Nostr public keys as network addresses instead of IP addresses. The concept was further developed during Arjun's time at Sovereign Engineering, a six-week Bitcoin and Nostr builder programme in Madeira that has produced projects like Blossom, Nutzaps, and TollGate itself (Sovereign Engineering).
FIPS reached its v0.1.0 alpha release in late February 2026. The source code is public (FIPS repository).
The Problem FIPS Solves
The modern internet is built on centralised infrastructure at every layer. Your ISP assigns your IP address. DNS servers translate domain names into those addresses. Certificate authorities validate who you are talking to. Every one of these is a single point of failure that can be pressured, subverted, or shut down.
During protests in Iran, the government cut domestic internet access to prevent communication among protesters. During the same period, BitChat usage (Jack Dorsey's Bluetooth mesh messaging app, launched July 2025) spiked in the country. Protesters could communicate internally, but they could not broadcast to the rest of the world. That communication blackout was deliberate and it worked.
FIPS is designed so that no single entity controls the network infrastructure.
How It Works
FIPS achieves this through three core design decisions that separate it from previous mesh networking attempts.
1. Nostr keys as network addresses. Every node on a FIPS network is identified by a Nostr public key (npub), not an IP address. This means your network identity is cryptographic, self-generated, and not assigned or controlled by any third party. The same key pair you use on Nostr for social interactions can be your address on the physical network. According to the FIPS design documentation, the system uses Nostr keypairs (secp256k1/schnorr) as native node identities, making every Nostr user a potential network participant.
2. Transport agnostic design. FIPS separates the routing layer from the physical transport layer. It does not care whether your connection is over WiFi, Bluetooth, Ethernet, a satellite uplink, or a serial cable.
"All you need to know is, I want to be able to send some data to a peer and I want to be able to get some data from a peer. I don't care how you get it there, just get it there." - Arjun (Citadel Dispatch Episode 193)
3. Full backwards compatibility with existing applications. This is the design decision that separates FIPS from every mesh project that came before it. FIPS includes a custom DNS server that, when any application on your computer requests an npub.fips address, returns a deterministic IPv6 address derived from that Nostr public key. The application then sends its traffic normally, and FIPS intercepts it at the network layer and routes it through the mesh. The application thinks it is using the regular internet. It has no idea it is on a mesh network.
"I looked at some of the other protocols and what I found is they often seem to expect everyone to re-implement all their applications to work with it. There is no way in hell you are going to get any adoption if everyone needs to rebuild their stack from scratch. There is forty years of history in libraries. Unless it works without any modification in all the applications, it is not going to fly." - Arjun
The Technical Underpinning
For those who want the detail, here is how FIPS handles the hard problems.
Every hop between peers is individually encrypted using the Noise Protocol Framework. On top of that, there is independent end-to-end encryption between the source and destination. This means intermediate nodes route packets without being able to read them, and they do not learn the Nostr identities of the endpoints. According to the FIPS design documentation, intermediate routers see only node_addrs, they can forward traffic without learning the Nostr identities of the endpoints.
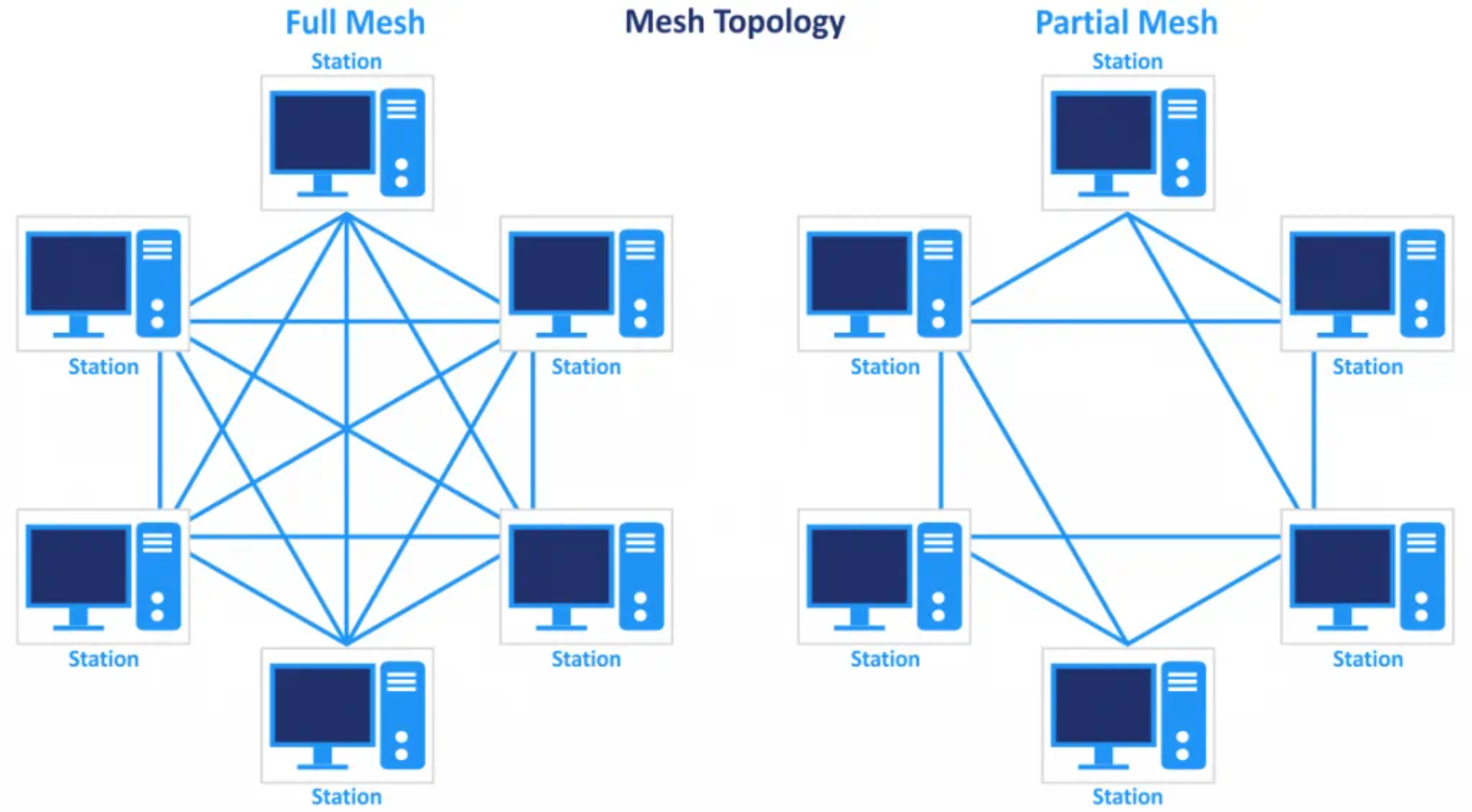
On local broadcast media like WiFi, a FIPS node broadcasts its presence and other nodes can discover it. Each peer holds a Bloom filter (a compressed data structure, currently one kilobyte) representing all the npubs it can reach. When you connect to a peer that can already reach 10,000 other nodes, it gives you this Bloom filter. When a packet arrives destined for any of those npubs, you know which peer to forward it to.
FIPS uses spanning tree coordinates and Bloom filter candidate selection. There are no global routing tables. The network self-organises and self-heals. If half the network fails, traffic routes around the failure through whatever transport is still available.
To send traffic to an endpoint, you need to know its npub. Intermediate nodes only see a node ID derived from the npub, not the npub itself. This means if your npub is not publicly known, it is difficult for an attacker to target you. Additionally, each peer rate-limits how many new connections it accepts simultaneously.
Why Is This Different from Every Previous Mesh Attempt
The mesh networking space is littered with failed projects and hype cycles. Gotenna turned out to be proprietary. LoRa devices have bandwidth limitations. BitChat, despite enormous initial excitement, left many users with nobody to talk to because you need neighbours running the same software.
FIPS differs in three ways that address historical failure points.
First, the backwards compatibility trick means adoption does not require app developers to change anything. If you run a Nostr relay on a FIPS network, any existing Nostr client can connect to it by adding an npub.fips address to its relay list. White Noise, Primal, Damus, any of them would work without modification. This dramatically lowers the bootstrapping barrier that killed previous mesh projects.
Second, FIPS works over existing internet infrastructure as an overlay. You do not need to wait for your physical neighbours to adopt it. Two people on opposite sides of the world can establish a FIPS peering connection over UDP right now, today, using the regular internet as transport. Then if the regular internet goes down, and they have local mesh connections, the mesh routes still work.
Third, economic incentives can be layered in. Arjun's other project, TollGate, allows WiFi routers to accept Bitcoin payments (via Cashu ecash) for internet access at rates as low as one sat per minute (TollGate). The vision is that FIPS routing could incorporate economic signals. If one link is expensive and another is cheap, routing decisions could factor in cost.
The Nostr Connection Runs Deep
Because all Nostr data is signed, it can be replicated and verified anywhere. Arjun described a scenario where a local community running FIPS has Nostr relays, Blossom servers (decentralised file storage), and Cashu mints operating entirely within the mesh. If the connection to the broader internet gets cut, everything inside the network keeps working. People can still chat on White Noise. They can still use Primal. They can still transact with ecash. When the connection is restored, the network gracefully reconciles, pulling in new data and pushing out what was created locally.
"Nostr allows us to completely remove the boundary between what is offline and online, it becomes a spectrum."
Traditional internet applications break when connectivity is lost because they assume a persistent connection to a server. Nostr applications, because they work with signed events that can be relayed and cached by any node, degrade gracefully. FIPS provides the networking layer that makes this graceful degradation work at the transport level as well.
The Privacy Implications for Bitcoin Users
FIPS does not make strong privacy claims in its current form. Arjun was clear that it is not onion-routed and that an observer with visibility over the entire network would still be able to analyse traffic patterns. However, the structural changes it introduces are significant.
Currently, running a Bitcoin node, a Lightning node, or a Cashu mint exposes you through the existing internet infrastructure. Your ISP knows your IP address. Your domain registrar knows who you are. DNS resolution creates logs. Certificate authorities can be compelled. As Arjun noted, "it is pretty hard to get a private domain, it is pretty hard to have a private IP address that is not linked to your identity."
On a FIPS network, none of these intermediaries exist. Your identity is a cryptographic key you generated yourself. Your network address is derived from that key. The connection between you and the person you are communicating with is encrypted end-to-end. There is no ISP to subpoena, no domain to seize, no certificate authority to compromise.
For Cashu mint operators specifically, Arjun raised an important point. Currently, a mint's identity is tied to its domain name. If that domain gets seized or the registrar caves to pressure, the mint effectively disappears from every wallet that had it configured. If mint identity were tied to an npub instead, the operator could rotate the underlying infrastructure without breaking the identity that users rely on.
Where It Stands Today
FIPS is at v0.1.0, which is alpha software. As of the Citadel Dispatch recording on March 6 2026, the network consisted of Arjun, Jonathan, and one or two other testers connecting to two public servers. The project needs testing, feedback, and code review from people with networking and cryptographic expertise.
The FIPS repository includes manuals for compiling and running nodes, Docker-based test meshes, and step-by-step guides. Arjun noted that packaging for OpenWRT routers is in progress, which would allow FIPS to run on commodity hardware.
The Lobsters community has already engaged with the project, comparing it to Yggdrasil (an overlay-only network that assumes existing TCP/IP infrastructure) and noting that FIPS is designed to operate at a lower level of the stack, making physical mesh networks possible.
Test it. Give feedback. Break it.